That looks like it’s just wrapping a WebView, is it not?
It looks like the CSS is just capping the container class width at 1440px, which has nothing to do with GTK
That looks like it’s just wrapping a WebView, is it not?
It looks like the CSS is just capping the container class width at 1440px, which has nothing to do with GTK
OP said it was to notify you when an alarm went off, not when it ran out of batteries.


If the code doesn’t change, the resulting docker image will have the same hash, and a new image won’t be created
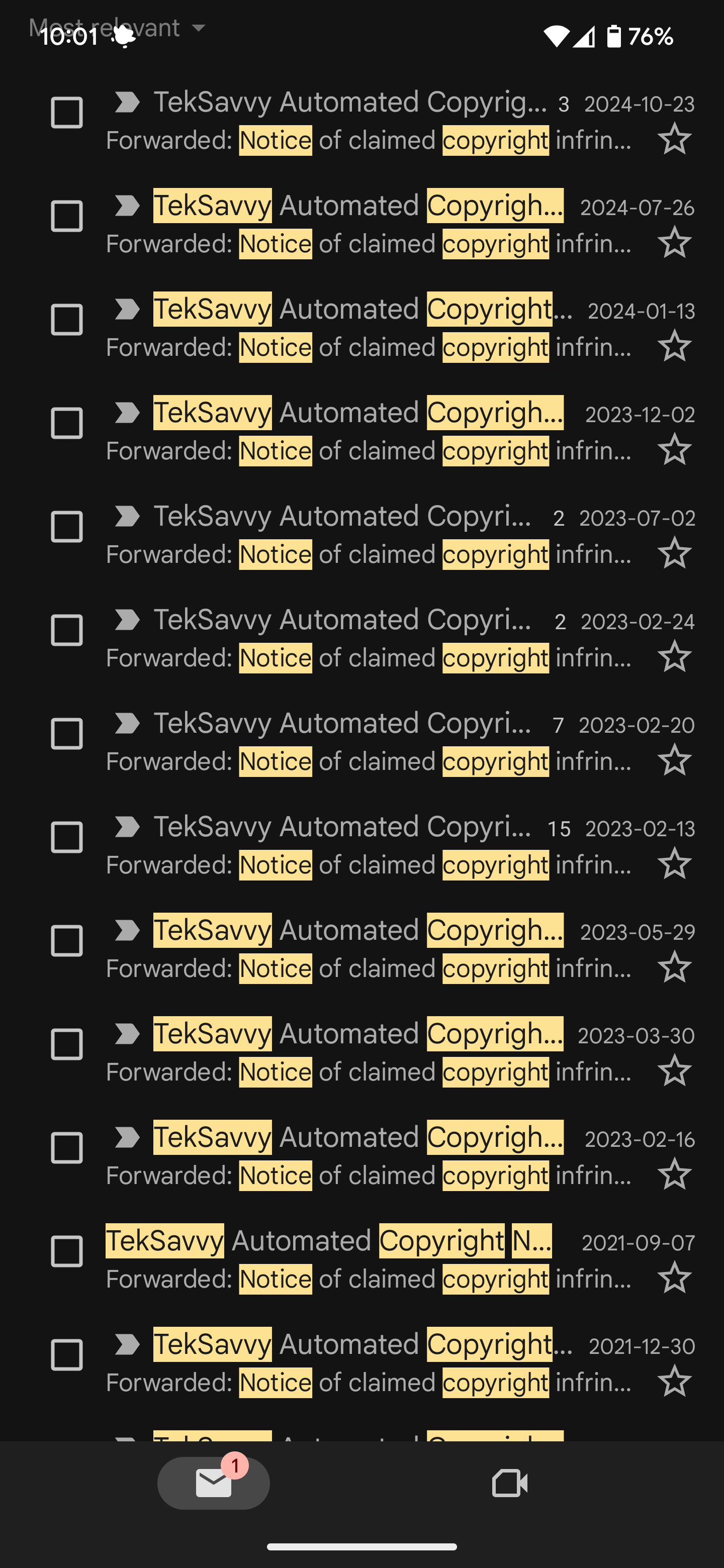
https://github.com/jackett/jackett/releases
Jackett is literally just releasing a new version every day


The content of the email is very laissez-faire, e.g. "we legally have to send these ¯\_(ツ)_/¯ "


I collect these like pokemon 🙃


Especially because it’s to a newbie, who stands to benefit the most from using an OS with more user share and more available online resources.


That assumes that an adversary has control of the browser
No it doesn’t, if they intercept an encrypted password over HTTPS they can resend the request from their own browser to get access to your account
The big reason you don’t want to send passwords over https is that some organizations have custom certs setup
What is the problem with that? The password is secure and only shared between you and the site you are intending to communicate with. Even if you sent an encrypted password, they wrote the client side code used to generate it, so they can revert it back to its plaintext state server side anyways
It is better to just not send the password at all.
How would you verify it then?
If not sending plaintext passwords was best practice then why do no sites follow this? You are literally posting to a site (Lemmy) that sends plaintext passwords in its request bodies to log-in


Client side verification is just security by obscurity, which gains you very little.
If someone is capable of MITM attacking a user and fetching a password mid-transit to the server over HTTPS, they are surely capable of popping open devtools and reverse engineering your cryptographic code to either a) uncover the original password, or b) just using the encrypted credentials directly to authenticate with your server without ever having known the password in the first place


You are acting like someone checked off a “log passwords” box, as if that’s a thing that even exists
Someone configured a logger to write HTTP bodies and headers, not realizing they needed to build a custom handler to iterate through every body and header anonymizing any fields that may plausibly contain sensitive information. It’s something that literally every dev has done at some point before they knew better.
More, but not way more - they would be licensing window IoT, not a full blown OS, and they wouldn’t be paying OTC retail rates for it.
If you know the key is composed of English language words you can skip strings of letters like “ZRZP” and “TQK” and focus on sequences that actually occur in a dictionary
You don’t memorize RSA keys
No im saying if your password size is limited to a fixed number of characters, as is the case with RSA keys, words are substantially less secure
“can you string words to form a valid RSA key”
“Yes this is the most secure way to do it”
“No, it’s not when there is a fixed byte length”
-> where we are now
we are talking about RSA keys - you don’t memorize your RSA keys
if you rely on memorizing all your passwords, I assume that means you have ample password reuse, which is a million times worse than using a different less-secure password on every site
Sure but we aren’t talking about that
You memorize your RSA keys?
We are talking about RSA though, so there is a fixed character length and it isn’t meant to be remembered because your private key is stored on disk.
Yes the word method is better than a random character password when length is unbounded, but creating secure and memorable passwords is a bit of an oxymoron in today’s date and age - if you are relying on remembering your passwords that likely means you are reusing at least some of them, which is arguably one of the worst things you can do.
Words are the least secure way to generate a password of a given length because you are limiting your character set to 26, and character N gives you information about the character at position N+1
The most secure way to generate a password is to uniformly pick bytes from the entire character set using a suitable form of entropy
Edit: for the dozens of people still feeling the need to reply to me: RSA keys are fixed length, and you don’t need to memorize them. Using a dictionary of words to create your own RSA key is intentionally kneecapping the security of the key.
Fair - point still stands though - the application only has a single breakpoint defined at 600sp from a cursory glance, the lack of an ultra-wide specific layout is just because it hasn’t been implemented rather than a shortfall of GTK (though I’m not sure you would even want to make the message view wider, as it would impair readability)